For many network engineers, building a spine-leaf data center fabric using technologies like VXLAN and BGP EVPN is a major milestone. The internal network delivers predictable latency, high bandwidth, and scalable east-west traffic forwarding.
However, once the internal fabric is operational, a new challenge quickly appears: how should the Internet edge be integrated into a spine-leaf architecture? Connecting firewalls, NAT gateways, and multiple Internet Service Providers (ISPs) to a Clos fabric introduces several design questions. Where should NAT be placed? Will ECMP break firewall state tables? What is the role of a Service Leaf? And how should multi-ISP routing be handled?
This guide explains practical spine leaf internet edge design patterns, including NAT placement strategies, service leaf architecture, and production-ready deployment models.
- Part 1: Understanding the Internet Edge — Border Leaf vs Service Leaf
- Part 2: Where Should NAT Be Placed in a Spine-Leaf Architecture
- Part 3: The ECMP Challenge — Preventing NAT Session Asymmetry
- Part 4: Multi-ISP Internet Edge Design
- Part 5: Moving from Lab to Production Infrastructure
- Part 6: Conclusion
- Part 7: Frequently Asked Questions
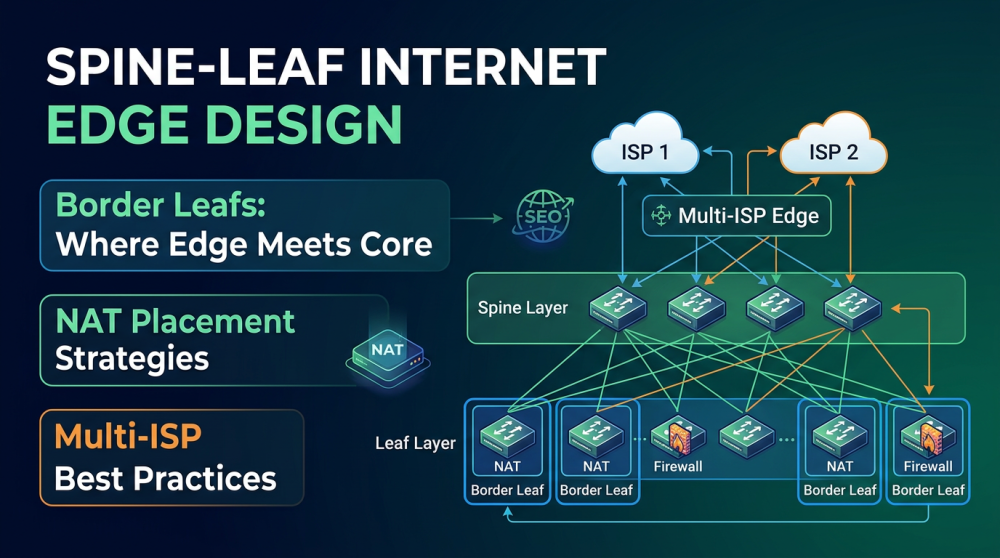
Part 1: Understanding the Internet Edge — Border Leaf vs Service Leaf
Traditional three-tier networks relied on core routers to handle Internet connectivity. In modern data centers, however, the spine layer should remain simple and stateless. Instead of attaching Internet connectivity to the spine, most modern fabrics introduce dedicated edge leaf roles.
Border Leaf
A Border Leaf is responsible for north-south traffic entering or leaving the data center fabric.
Typical responsibilities include:
- terminating VXLAN tunnels
- routing traffic toward external networks
- connecting to WAN or Internet routers
- supporting VRF-Lite or eBGP handoff
Border Leafs are usually deployed in redundant pairs to maintain high availability.
Service Leaf
A Service Leaf is designed to host Layer 4–7 network appliances, including:
- firewalls
- load balancers
- IPS systems
- NAT gateways
Traffic from the fabric is redirected to these appliances for security inspection or translation before reaching the Internet. In many enterprise deployments, Border Leaf and Service Leaf roles are combined on the same switches to simplify the topology.
Part 2: Where Should NAT Be Placed in a Spine-Leaf Architecture?
One of the most common design questions is whether NAT should run on the border router or the firewall.
Best practice in modern enterprise data centers is to perform NAT on the firewall connected to the Service Leaf layer.
Security and Translation in the Same Control Point
Firewalls already perform security inspection. Placing NAT on the firewall ensures that public addresses map directly to inspected traffic and that policy enforcement and translation occur together.
VRF Stitching Model
Many designs use a VRF stitching architecture, sometimes called a firewall sandwich.
Example traffic flow:
Inside VRF (VXLAN tenant network)
|
Firewall (inspection + NAT)
|
Outside VRF (Internet edge)Traffic from the internal tenant VNI is routed to the firewall, inspected, NAT-translated, and then forwarded to the external routing domain.
Part 3: The ECMP Challenge — Preventing NAT Session Asymmetry
Spine-leaf networks rely heavily on Equal-Cost Multi-Path (ECMP) routing to distribute traffic across multiple links.
However, NAT and firewalls are stateful systems and must observe both directions of a connection.
If ECMP hashes outbound traffic through Firewall A and return traffic through Firewall B, the session may fail. This is known as asymmetric routing.
Deploy Stateful Firewall Clusters
Most enterprise firewalls support state synchronization between nodes. Active-standby or active-active clusters replicate NAT tables and connection state so sessions survive failover.
Apply Source NAT (SNAT)
When exposing internal services to the Internet, SNAT ensures the return path goes back to the same firewall interface rather than relying on ECMP hashing.
Use Deterministic Routing Policies
Routing policies such as BGP local preference, policy-based routing, or traffic pinning can ensure symmetric paths through the firewall layer.
Part 4: Multi-ISP Internet Edge Design
Production environments usually require multiple Internet providers for redundancy and traffic engineering.
A typical multi-ISP data center edge architecture may follow this structure:
Fabric Leaf
|
Service Leaf
|
Firewall Cluster
|
Border Routers
|
ISP 1 / ISP 2Border Routers
Dedicated edge routers connect directly to ISPs and handle BGP peering, route filtering, and Internet routing tables.
VRF-Lite Handoff
Border routers commonly connect to the Service Leaf using VRF-Lite trunks to separate internal tenant networks from external routing domains.
Firewall NAT Pools
Firewalls maintain separate NAT address pools for different ISPs. Policy-based routing or BGP weighting can determine which provider handles specific traffic flows.
Default Route Injection
Border routers advertise a default route toward the firewall layer. After applying NAT and security policies, the firewall redistributes the route back into the EVPN fabric.
Part 5: Moving from Lab to Production Infrastructure
Many engineers experiment with spine-leaf designs in virtual labs before deploying real hardware. Production environments introduce additional requirements.
Spine and Leaf Switches
These switches must support:
- VXLAN hardware encapsulation
- BGP EVPN control plane
- high-speed interfaces such as 25G or 100G
Border Routers
Edge routers should provide strong BGP processing capability, large routing tables, and deep packet buffers.
Firewall Appliances
Next-generation firewalls must support high-throughput NAT, deep packet inspection, and redundancy clustering.
Enterprise deployments often source switching and routing platforms through Router-switch, which provides hardware used in large-scale spine-leaf and Internet edge architectures.
During planning phases, engineers frequently compare device specifications and availability using tools like IT-Price when evaluating equipment for large network deployments.
Part 6: Conclusion
Integrating Internet connectivity into a spine-leaf fabric requires careful architectural planning.
By separating core fabric forwarding from stateful services such as NAT and firewall inspection, organizations can maintain the scalability advantages of a Clos network while still supporting secure Internet access.
Successful deployments typically rely on several key principles:
- isolate services using service leaf architecture
- place NAT on firewall tiers
- manage ECMP behavior carefully
- implement deterministic routing policies
- design for multi-ISP redundancy
With the right architecture, the Internet edge can scale alongside the data center fabric while maintaining high performance and operational stability.
Part 7: Frequently Asked Questions
Q1.Where should NAT be placed in a spine-leaf architecture?
In most enterprise deployments, NAT is implemented on the firewall connected to the service leaf layer. This allows security inspection and address translation to occur at the same control point.
Q2.What is a service leaf in a spine-leaf network?
A service leaf is a leaf switch dedicated to hosting network service appliances such as firewalls, load balancers, and intrusion prevention systems.
Q3.Why can ECMP cause problems for NAT?
ECMP distributes traffic across multiple paths. If outbound traffic goes through one firewall and return traffic arrives through another, the firewall may drop the session because it does not recognize the state.
Q4.How do enterprises support multiple ISPs in a data center fabric?
Enterprises typically deploy border routers that connect to multiple ISPs using BGP. Firewalls connected to the service leaf layer perform NAT and security inspection before traffic enters or leaves the data center.

Expertise Builds Trust
20+ Years • 200+ Countries • 21500+ Customers/Projects
CCIE · JNCIE · NSE7 · ACDX · HPE Master ASE · Dell Server/AI Expert




















































































































