Shop By Categories
- Routers
- AR G3 Routers
- Enterprise Integrated Branch Routers
- Service Provider Edge Routers
- Cisco ASR 9000 Router
- Cisco ASR 5000 Series
- Cisco 10000 Routers
- Cisco 12000 Routers
- Huawei NE05E/08E Routers
- Huawei NetEngine 8000 Routers
- Huawei NetEngine20E-S Routers
- Huawei NetEngine40E Routers
- Huawei NetEngine5000E Routers
- Juniper MX10003/MX10008/MX10016 Routers
- Juniper MX150 Routers
- Juniper MX2000 Routers
- Juniper MX204/MX240/MX480 Routers
- Juniper MX960 5G Universal Routing Platforms
- Juniper PTX1000/3000/5000/10000 Routers
- Juniper SRX Service Gateways
- Cisco Catalyst 8200 Series Edge Platforms & uCPE
- Small Business Routers
- Cisco 1100 ISR
- Cisco 1800 ISR
- Cisco 2800 ISR
- Cisco 3800 ISR
- Cisco 800 ISR
- Cisco 900 ISR
- Cisco RV Routers
- Huawei AR100 Enterprise Routers
- Huawei AR200 Enterprise Routers
- Huawei AR530 Agile Gateways
- Huawei ME60 Control Gateways
- Huawei NetEngine AR6000 Enterprise Routers
- Juniper CTP150 & CTP2000 Platforms
- Juniper MX Base Product Bundles
- Ubiquiti Enterprise Routers
- WAN Aggregation and Internet Edge Routers
- Industrial Routers
- Cisco Routers
- Cisco Router ISR 4000 hot
- Cisco Router ISR 1900
- Cisco Router ISR 2900
- Cisco Router ISR 3900
- Cisco Router ISR 1100
- Cisco Router ISR 800
- Cisco Router ISR 900
- Cisco Router ASR 900
- Cisco Router ASR 1000
- Cisco Catalyst 8200 Series Edge Platforms & uCPE
- Cisco Router ASR 5000
- Cisco Router ASR 9000
- Cisco 8000 Series Routers
- Cisco Router 10000 Series
- Cisco Router 12000 Series
- Cisco Router ISR 1800
- Cisco Router ISR 2800
- Cisco Router ISR 3800
- Cisco Router 7200 Series
- Cisco Router 7600 Series
- Cisco Industrial Routers
- Modules
- Cisco Catalyst 8000 Series Appliances
- Cisco Router NCS 6000
- Cisco Router NCS 5000
- Cisco Router NCS 4000
- Cisco Router NCS 2000
- Cisco Router NCS 1000
- Cisco Router NCS 540
- Cisco Gateway
- Cisco Routers CBR Series
- Huawei Routers
- AR1200 Series Enterprise Routers
- AR2200 Series Enterprise Routers
- AR3200 Series Enterprise Routers
- AR3600 Series Enterprise Routers
- AR6000 Series Enterprise Routers
- Huawei NetEngine Series Routers
- NetEngine 8000 Universal Service Routers
- NE05E/08E Series Mid-range Service Routers
- NetEngine20E-S Series Universal Service Routers
- NetEngine40E Series Universal Service Routers
- NetEngine5000E Cluster Routers
- NetEngine80E Series Universal Service Routers
- NE05E/08E Series Routers Software
- NE05E/08E Series Routers Accessories
- NE20E-X6 Series Universal Service Router
- NetEngine 8000 Universal
- Huawei Multi-Service Control Gateways
- AR100 Series Enterprise Routers
- AR120 Series Enterprise Routers
- AR150 Series Enterprise Routers
- AR160 Series Enterprise Routers
- AR200 Series Enterprise Routers
- AR530 Series Agile Gateways
- Huawei AR550 Series Agile Gateways
- Huawei AR502H Series Edge Computing IoT Gateways
- Huawei AR502 Series Industrial Routers
- Huawei AR509 Series IoT Gateways
- AR600 Series Enterprise Routers
- AR500 Series Enterprise Routers
- Juniper Routers
- Juniper CTP150 & CTP2000 Platforms
- Juniper MX10003/MX10008/MX10016 Routers
- Juniper MX2020 5G Universal Routing Platforms
- Juniper MX960 5G Universal Routing Platforms
- Juniper PTX1000/3000/5000/10000 Routers
- Juniper Other Routers
- Juniper Router Modules & Cards
- Juniper Router Licenses
- Juniper Routers Services
- Juniper Router Accessories
- Juniper PTX1000
- D-Link Routers
- Ubiquiti Routers
- Mikrotik Routers
- Ruijie Routers
- H3C Routers
- Switches
- Centec Communications
- Access Switches
- Cisco Catalyst 9200 Switches
- Cisco Catalyst 9300 Switches
- Cisco Catalyst 9400 Switches
- HPE Aruba 1820 Switches
- HPE Aruba 1850 Switches
- HPE Aruba 1920S Switches
- HPE Aruba 1950 Switches
- HPE Aruba 2530 Switches
- HPE Aruba 2540 Switches
- HPE Aruba 2920 Switches
- HPE Aruba 2930F Switches
- HPE Aruba 2930M Switches
- Cisco Catalyst 2960 Switches
- Cisco Catalyst Compact Switches
- Cisco Catalyst Micro Switches
- Cisco Catalyst 3850 Switches
- Dell Networking N1500 Switches
- Dell Networking X Switches
- HPE 1410 Switches
- HPE 1420 Switches
- HPE 1620 Switches
- HPE 1810 Switches
- HPE 2615 Switches
- HPE 2620 Switches
- HPE 2915 Switches
- HPE 3500 and 3500 yl Switches
- Huawei S2300 Switches
- Huawei S3300 Switches
- Huawei S3700 Switches
- Juniper EX2300 Ethernet Switches
- Juniper EX3400 Ethernet Switches
- D-Link Access Switches
- Dell EMC Networking PowerSwitch N2200 Series
- Dell EMC Networking PowerSwitch N3200 Series
- Dell EMC PowerSwitch N1100 Series
- H3C Access Switches
- Extreme Access Switches
- SMB Switches
- D-link SMB Switches
- HPE Aruba OfficeConnect Switches
- HPE Aruba Instant On 1930 Switches
- Cisco Business 110 Series Unmanaged Switches
- Cisco 110 Unmanaged Switches
- Cisco 200 Smart Switches
- Cisco 220 Smart Switches
- Cisco 300 Managed Switches
- Cisco 250 Smart Switches
- Cisco 350 Managed Switches
- Cisco 350X Stackable Managed Switches
- Cisco 500 Stackable Managed Switches
- Cisco 550X Stackable Managed Switches
- Huawei S1700 Switches
- Huawei S2700 Switches
- Ubiquiti Enterprise Switches
- Extreme SMB Switches
- Cisco Business 220 Series Smart Switches
- Cisco Business 350 Series Managed Switches
- Convergence Switches
- Huawei S5700 Enterprise Switches
- Juniper EX4300 Ethernet Switches
- HPE Aruba 3810 Switches
- HPE Aruba 5400R Switches
- Cisco Catalyst 2960-X/XR Switches
- Cisco Catalyst 3650 Switches
- Cisco Catalyst 3850 Switches
- Cisco Catalyst 2960 Switches
- Cisco Catalyst 3750 Switches
- Cisco Catalyst 4900 Switches
- Dell Networking N3000 Switches
- HPE 5500 HI Switches
- HPE 5510 HI Switches
- HPE FlexFabric 5700 Switches
- HPE FlexFabric 5800 Switches
- HPE FlexFabric 5900 Switches
- HPE FlexFabric 5930 Switches
- HPE FlexFabric 5940 Switches
- HPE FlexNetwork 5120 SI Switches
- HPE FlexNetwork 5130 HI Switches
- Huawei S6300 Enterprise Switches
- Juniper EX4600 Ethernet Switches
- Huawei S5300 Enterprise Switches
- Huawei S6700 Enterprise Switches
- Core and Distribution Switches
- Cisco Catalyst 9600 Switches
- HPE Aruba 8320 Switches
- Cisco Catalyst 4500-X Series
- Cisco Catalyst 6500 Series
- Cisco Catalyst 6800 Series
- Cisco Catalyst 9500 Switches
- Cisco Catalyst 4500 Switches
- Dell Networking N4000 Switches
- HPE FlexNetwork 10500 Switches
- Huawei S12700 Switches
- Huawei S7700 Switches
- Huawei S9300 Switches
- Huawei S9700 Switches
- Juniper QFX3000 Switches
- Juniper QFX5100 Switches
- D-Link Core Switches Series
- H3C Core Switches
- Data Center Switches
- Cisco Nexus 2000 Switches
- Cisco Nexus 3000 Switches
- Cisco Nexus 5000 Switches
- Cisco Nexus 7000 Switches
- Cisco Nexus 9000 Switches
- Huawei CloudEngine 12800 Data Center Switches
- Huawei CloudEngine 16800 Data Center Switches
- Huawei CloudEngine 5800 Data Center Switches
- Huawei CloudEngine 6800 Data Center Switches
- Huawei CloudEngine 7800 Data Center Switches
- Huawei CloudEngine 8800 Data Center Switches
- Dell Networking S4048-ON Switches
- D-Link Data Center Switches
- Dell EMC PowerSwitch S series 1GbE switches
- Extreme Data Center Switches
- Industrial Ethernet Switches
- Aggregation Switches
- Edge Switches
- Cisco Switches
- Cisco Switch Catalyst 9200
- Cisco Switch Catalyst 9300
- Cisco Switch Catalyst 9400
- Cisco Switch Catalyst 9500
- Cisco Switch Catalyst 9600
- Cisco Switch Catalyst 1000
- Cisco Switch Catalyst 3850
- Cisco Switch Catalyst 3650
- Cisco Switch Catalyst 2960
- Cisco Catalyst Micro Switches
- Cisco Catalyst Compact Switch
- Cisco Nexus 3000 Series
- Cisco Nexus 5000 Series
- Cisco Nexus 9000 Series
- Cisco Nexus 7000 Series
- Cisco Industrial Ethernet 1000 Switches
- Cisco Catalyst IE3000 Rugged Switches
- Cisco Industrial Ethernet 2000 Switches
- Cisco Industrial Ethernet 4000 Switches
- Cisco Industrial Ethernet 5000 Switches
- Cisco Switch Catalyst 4500
- Cisco Switch Catalyst 4900
- Cisco Switch Catalyst 6800
- Cisco Switch Catalyst 3560
- Cisco Switch Catalyst 3750
- Cisco Switch Catalyst 6500
- Cisco Nexus 2000 Series
- Cisco Catalyst IE9300 Rugged Series
- Cisco Catalyst IE9311 Rugged Series
- Cisco Catalyst IE9315 Rugged Series
- Cisco Catalyst IE9316 Rugged Series
- Cisco Catalyst IE9317 Rugged Series
- Cisco Catalyst IE9318 Rugged Series
- Cisco Catalyst IE9319 Rugged Series
- Cisco Catalyst IE9320 Rugged Series
- Cisco Catalyst IE9321 Rugged Series
- Cisco Catalyst IE9322 Rugged Series
- Cisco Catalyst IE9323 Rugged Series
- Cisco Catalyst 1300 Series Switches
- Cisco Catalyst 1200 Series Switches
- Adapters
- Cisco Meraki Series Switches
- Cisco Industrial Ethernet 3000 Switches
- Cisco MDS Series Switches
- FC Switches
- HPE Aruba Switches
- HPE Aruba Networking Switches
- HPE Aruba 8360 Series Switches
- HPE Aruba 8400 Series Switches
- HPE Aruba 2930F Series Switches
- HPE Aruba Instant On 1930 Switches
- HPE Aruba 2530 Series Switches
- HPE Aruba 2920 Series Switches
- HPE Aruba 3810 Series Switches
- HPE Aruba 2540 Series Switches
- HPE Aruba 2930M Series Switches
- HPE Aruba 5400R Series Switches
- HPE Aruba 8320 Series Switches
- HPE Aruba Switch v3 Modules
- HPE Aruba Switch v2 Modules
- HPE Aruba Switches Transceivers
- HPE Aruba Switch Accessories
- HPE Aruba OfficeConnect Switches
- HPE Aruba 2615 Switches
- HPE Aruba 2620 Switches
- HPE Aruba 2915 Switches
- HPE Aruba 6400 Series Switches
- HPE Aruba 6100 Series Switches
- HPE Aruba 6300M Series Switches
- HPE Aruba 6200F Series Switches
- HPE Aruba 6000 Series Switches
- HPE Aruba Switches Accessories
- HPE Aruba 6300M Series Switches
- HPE Aruba 6300F Series Switches
- HPE Aruba 8320 Series Switches
- HPE Aruba 9300S Series Switches
- HPE Aruba Data Center Switches
- HPE Aruba ProCurve Switches
- HPE 10500 Switches
- HPE FlexNetwork 5130 EI Switches
- HPE FlexNetwork 5130 HI Switches
- HPE FlexNetwork 5120 SI Switches
- HPE 5500 EI Switches
- HPE 5500 HI Switches
- HPE Aruba Procurve Switch Transceivers
- HPE 5510 HI Switches
- HPE Aruba 1900 Switches
- HPE 3500 and 3500 yl Switches
- HPE 1950 Switches
- HPE Aruba 1920 Switches
- Aruba 1900 Switches
- HPE 1820 Switches
- HPE Aruba 1810 Switches
- HPE Aruba 1620 Switches
- HPE 1420 Switches
- HPE Aruba 1410 Switches
- HPE 55xx Modules
- HPE 35xx Switch Modules
- HPE Aruba 1620 Switches
- HPE Aruba 1900 Switches
- HPE Aruba 1410 Switches
- HPE Aruba Networking Switches
- Dell Switches
- Dell Networking X Series Switches
- Dell Networking N1500 Switches
- Dell Networking N3000 Switches
- Dell Networking N4000 Switches
- Dell Networking S4048-ON Switches
- Dell Networking S4100-ON Switches
- Dell Networking S3000-ON Switches
- Dell Networking N1000 Switches
- Dell Networking N2000 Switches
- Dell KVM Switches
- Dell EMC Networking PowerSwitch N2200 Series
- Dell EMC Networking PowerSwitch N3200 Series
- Dell EMC PowerSwitch N1100 Series
- Dell EMC PowerSwitch S series 1GbE switches
- Huawei Switches
- Huawei S1700 Series Switches
- Huawei S2700 Series Switches
- Huawei S3700 Series Switches
- Huawei S5700 Series Switches
- Huawei S5700S Series Switches
- Huawei S6700 Series Switches
- Huawei S7700 Series Switches
- Huawei S9700 Series Switches
- Huawei S12700 Series Switches
- Huawei Data Center Switches
- Huawei S2300 Series Switches
- Huawei S3300 Series Switches
- Huawei S5300 Series Switches
- Huawei S6300 Series Switches
- Huawei S9300 Series Switches
- Huawei Data Center Switches
- Huawei S16700 Series Switches
- Huawei S8700 Series Switches
- Juniper Switches
- Juniper EX4300 Series Ethernet Switches
- Juniper EX2300 Series Ethernet Switches
- Juniper EX4600 Series Ethernet Switches
- Juniper EX3400 Series Ethernet Switches
- Juniper EX3300 Series Ethernet Switches
- Juniper QFX5200 Series Switches
- Juniper QFX5100 Series Switches
- Juniper QFX3000 Series Switches
- Juniper Switch Modules & Cards
- Juniper Switch Licenses
- Ruckus Switches
- D-Link Switches
- D-Link Smart Switches
- D-Link Unmanaged Switches
- D-Link Fully Managed Switches
- D-Link Access Switches
- D-Link Aggregation Switches
- D-Link Core Switches Series
- D-Link Data Center Switches
- D-Link Intelligent Network Management Switches
- D-Link Industrial Switches
- D-Link Add Points Switches
- D-Link Wired Network Cards
- D-Link Switch Accessories
- Ubiquiti Switches
- H3C Switches
- Extreme Switches
- ExtremeSwitching 200 Series
- ExtremeSwitching X440-G2 Series
- ExtremeSwitching X460-G2 Series
- ExtremeSwitching X670-G2 Series
- ExtremeSwitching X695 Series
- ExtremeSwitching VSP 7400 Series
- Extreme Networks A-Series Switches
- Extreme Networks S-Series Switches
- ExtremeSwitching 8000 Series
- Extreme Switches Modules & Cards
- Extreme Switches Licenses
- Extreme Switches Accessories
- Extreme Summit X430 Series
- Alcatel-Lucent Switches
- Mikrotik Switches
- Arista Switches
- Arista 7050X Series Switches
- Arista 7010T Series Switches
- Arista 720XP Series Switches
- Arista 7150 Series Switches
- Arista 7280R Series Switches
- Arista 7130 Series Switches
- Arista 7020R Series Switches
- Arista 7170 Series Switches
- Arista 7160 Series Switches
- Arista Switches Accessories
- Arista 7500R Series Universal Spine Platform
- Arista 7208R Series Ethernet Universal Leaf Platform
- NVIDIA Mellanox Switches
- Broadcom Switches
- Nvidia Switches
- Ruijie Switches
- MRD Switches
- H3C Switches
- MRD
- Arisla Switches
- Brocade Switches
- Firewalls
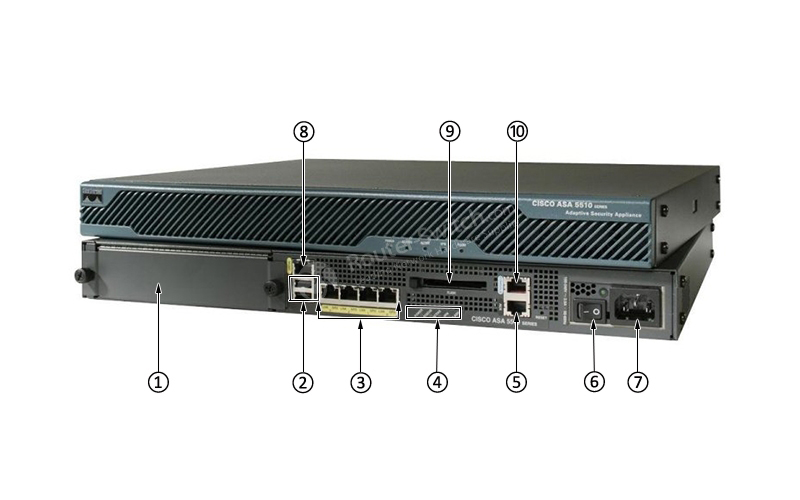
- Cisco ASA 5500 Series
- Cisco Firepower 1000 Series
- Cisco Firepower 2100 Series
- Cisco Firepower 4100 Series
- Cisco Firepower 7000 Series
- Cisco Firepower 8000 Series
- Cisco Firepower 9300 Series
- Cisco ISA 500 Series
- Cisco Meraki MX Appliances
- HPE Aruba Clearpass
- Huawei Application Security Gateways
- Huawei Data Center Firewalls
- Huawei DDoS Protection Systems
- Huawei Next-Generation Firewalls
- Huawei Security Platforms
- Juniper SRX Service Gateways
- Cisco Firewalls
- Cisco ASA 5500 Series
- Cisco Firepower 1000 Series Appliances
- Cisco Firepower 2100 Series Appliances
- Cisco Firepower 4100 Series Appliances
- Cisco Firepower 7000 Series Appliances
- Cisco Firepower 8000 Series Appliances
- Cisco Firepower 9300 Series Appliances
- Cisco ISA 500 Series
- Cisco Firepower Appliance Accessories
- Cisco Firepower 3100 Series Appliances
- Cisco Firepower 4200 Series Appliances
- Cisco Firepower 9000 Series Appliances
- Cisco Secure Web Appliance
- Cisco ISE
- Cisco Secure Endpoint
- Alteon
- Accessories
- Email Security Appliance
- Cisco Firepower 4000 Series Appliances
- Juniper Security
- H3C Firewalls
- Dell Firewalls
- Huawei Firewalls
- Sonicwall Firewalls
- Palo Alto Firewalls
- Palo Alto PA-5000 Series Firewalls
- Palo Alto PA-5400 Series Firewalls
- Palo Alto PA-400 Series Firewalls
- Palo Alto PA-3200 Series Firewalls
- Palo Alto Next-generation Firewalls
- Palo Alto PA-5200 Series Firewalls
- Palo Alto PA-800 Series Firewalls
- Palo Alto PA-7000 Series Firewalls
- Palo Alto PA-3000 Series Firewalls
- Palo Alto Firewalls ION Devices
- Palo Alto Firewalls Appliance
- Palo Alto PA-3400 Series Firewalls
- Palo Alto PA-1400 Series Firewalls
- Ubiquiti Firewalls
- Check Point Firewalls
- Ruijie Firewalls
- Ruijie Security
- A10 Firewalls
- Hillstone Firewalls
- Hillstone
- Sophos Firewalls
- WatchGuard Firewalls
- Wireless
- Indoor Access Points
- WiFi 6 Access Points
- Cisco Catalyst 9100 WiFi 6 Access Points
- Juniper Mist WiFi 6 Access Points
- HPE Aruba 500H Hospitality WiFi-6 Access Points
- HPE Aruba 550 WiFi-6 Access Points
- HPE Aruba 530 WiFi-6 Access Points
- HPE Aruba 500 WiFi-6 Access Points
- HPE Aruba 510 Series Access Points
- Huawei AirEngine WiFi 6 Access Points
- Ruckus WiFi 6 Access Points
- H3C WiFi 6 Access Points
- Extreme WiFi 6 Access Points
- 802.11ac Wave 2 Access Points
- Cisco 1800 Access Points
- Cisco 2800 Access Points
- Cisco 3800 Access Points
- Cisco 4800 Access Points
- Huawei 802.11ac Wave 2 Access Points
- Ruckus 802.11ac Wave 2 Access Points
- HPE Aruba Instant On Indoor Access Points
- HPE Aruba 200 Series Access Points
- HPE Aruba 300 Series Access Points
- H3C 802.11ac Access Points
- Extreme 802.11ac Wave 2 Access Points
- Ruckus 802.11ac Wave 3 Access Points
- WiFi 6 Access Points
- Outdoor Access Points
- Cisco 1560 Outdoor Access points
- Cisco 1570 Outdoor Access Points
- Cisco Catalyst IW6300 Series Heavy Duty Access Points
- HPE Aruba 570 Outdoor WiFi-6 Access Points
- HPE Aruba 570EX Outdoor WiFi-6 Access points
- HPE Aruba 518 Ruggedized Access Points
- HPE Aruba 370 Series Outdoor WiFi 5 Access Points
- HPE Aruba 360 Series Outdoor WiFi 5 Access Points
- Huawei AirEngine WiFi 6 Outdoor Access Points
- Huawei 8000 Outdoor Access Points
- Ruckus Outdoor Access Points
- Ubiquiti Outdoor Access Points
- Cisco Catalyst 9124 WiFi 6 Outdoor AP
- Remote Access Points
- SMB Access Points
- WLAN Controllers
- Wireless Bridges
- Access Point Antennas
- Cisco Wireless APs & Controllers
- Cisco WLAN Controller
- Cisco 1810 Access Point
- Cisco 1810W Access Point
- Cisco 1815 Access Point
- Cisco 1830 Access Point
- Cisco 1840 Access Points
- Cisco 1850 Access Point
- Cisco 2800 Access Point
- Cisco 3800 Access Point
- Cisco 4800 Access Point
- Cisco Catalyst 9100 WiFi 6 Access Point
- Cisco Catalyst IW6300 Series Heavy Duty Access Points
- Cisco 1560 Outdoor Access points
- Cisco 1570 Outdoor Access Point
- Cisco Antenna 2.4 5 5.8 GHz
- Cisco 1700 Access Point
- Cisco 2700 Access Point
- Cisco 3700 Access Point
- Cisco 1600 Access Point
- Cisco 2600 Access Point
- Cisco 3600 Access Point
- Cisco 1520 Mesh Access Point
- Cisco 1530 Outdoor Access point
- Cisco 1550 Access Point
- Cisco 3500 Access Point
- AP and Bridge Accessories
- Cisco 521 Access Point
- Cisco 600 Access Point
- Cisco 700 Access Point
- Cisco 1130 Access Point
- Cisco 1140 Access Point
- Cisco 1240 Access Point
- Cisco 1250 Access Point
- Cisco 1260 Access Point
- Cisco 1310 Access Point Bridge
- Cisco 1040 Access Point
- Cisco 1410 Series Bridge
- Mobility Services Engine
- HPE Aruba Wireless
- HPE Aruba Access Points
- Aruba Instant On Indoor Access Points
- Aruba 510 Series Access Points
- Aruba 100 Series Access Points
- Aruba 200 Series Access Points
- Aruba 300 Series Access Points
- Aruba OfficeConnect Series Access Points
- Aruba 500 Series Access Points
- HPE MSM400 Series Access Points
- HPE 400 Series Access Points
- M330 Access Points
- Aruba AP Antennas
- Aruba 500H Hospitality WiFi-6 Access Points
- Aruba 550 WiFi-6 Access Points
- Aruba 530 WiFi-6 Access Points
- Aruba 500 WiFi-6 Access Points
- Aruba 570 Outdoor WiFi-6 Access Points
- Aruba 570EX Outdoor WiFi-6 Access points
- Aruba 518 Ruggedized Access Point
- Aruba 560 WiFi-6 Access Points
- Aruba Access Points Accessory
- Aruba Other Access Points
- Aruba 200 Series Access Points
- Aruba 100 Series Access Points
- Aruba 300 Series Access Points
- Aruba M330 Access Points
- Aruba OfficeConnect Series Access Points
- HPE Aruba Controllers
- HPE Aruba Security Management
- HPE Aruba Controller Licenses
- HPE Aruba Controllers Licenses
- HPE Aruba Access Points
- Huawei Wireless
- Juniper Wireless
- Ruckus Wireless
- D-Link Wireless
- Ubiquiti Wireless
- Extreme Wireless
- Alcatel-Lucent Wireless
- H3C Wireless
- Mikrotik Wireless
- Ruijie Wireless
- Ruckus Wireless APs
- Cisco Wireless
- Indoor Access Points
- Unified Communications
- Networking Accessories
- Modules & Cards
- Cisco Modules & Cards
- Cisco Catalyst 9000 Switch Modules
- Cisco ASR 1000 Router Modules & Interfaces
- Cisco Firewalls Modules & Cards
- Router EHWIC WAN Cards
- Router WIC WAN Cards
- VIC VIC2 VIC3 Voice Cards
- Router VWIC2 VWIC3 Cards
- NM NME EM Network Modules
- PVDM Voice/FAX Modules
- Router AIM Modules
- Router ISR G2 SM ISM Modules
- Cisco 8000 Series Routers Modules & Cards
- Cisco 6800 Switch Modules
- Cisco Nexus 3000 Switch Modules & Cards
- Cisco Nexus 5000 Switch Modules
- Cisco Nexus 7000 Switch Modules & Cards
- Cisco Nexus 9000 Switch Modules & Cards
- Cisco 4500 Switch Modules
- Cisco 6500 Switch Modules
- Cisco Wireless Services Module
- Cisco 7200 Modules
- Cisco 7600 Modules
- Cisco IE Switch Modules & Cards
- Cisco Controller Modules
- Cisco Catalyst 8000 Series Edge Platforms Modules & Cards
- Cisco ISR 4000 Router Modules & Cards
- Cisco Optics Modules
- Cisco Memory & Flash
- Dell Optical Transceivers
- HPE Transceivers
- Huawei Optical Transceivers
- Huawei Modules & Cards
- Juniper Transceivers
- D-Link Optical Transceivers
- Ubiquiti Modules
- Extreme Networks Transceivers
- Alcatel-Lucent Transceivers
- Kingston Accessories
- NVIDIA Mellanox Network Cards
- NVIDIA Mellanox Modules
- HPE Aruba Transceivers
- Broadcom Accessories
- Intel Accessories
- QLOGIC Accessories
- EMULEX Accessories
- Kingston Accessories
- Ruijie Modules & Cards
- Hillstone Modules & Cards
- Palo Alto Modules & Cards
- Cisco Modules & Cards
- Power Supplies, Cables and Other
- Cisco Cables Accessories
- Cisco Power Supply
- Catalyst 3650 Switch Power Supply
- Catalyst 3850 Switch Power Supply
- Catalyst 9000 Switch Power Supply
- Catalyst 3560 Switch Power Supply
- Catalyst 4500 Switch Power Supply
- 800 Router Power Supply
- ASR Router Power Supply
- ISR Router Power Supply
- Nexus Switches Power Supply
- IE Switch Power Supply
- Wireless Products Power Supply
- Cisco Accessories
- Other Cisco Products
- HPE Accessories
- Dell Accessories
- Huawei Accessories
- Huawei Router Accessories
- Huawei Switch Accessories
- S5700 Series Switch Accessories
- S5300 Series Switch Accessories
- CE8800 Series Switch Accessories
- CE7800 Series Switch Accessories
- CE6800 Series Switch Accessories
- CE5800 Series Switch Accessories
- S12700 Series Switch Accessories
- S9700 Series Switch Accessories
- S9300 Series Switch Accessories
- S7700 Series Switch Accessories
- S6700 Series Switch Accessories
- CE12800 Series Switch Accessories
- Huawei Firewall Security Accessories
- Huawei Antennas & Accessories
- Huawei Camera Accessories
- Ubiquiti Accessories
- Extreme Networks Accessories
- Extreme Networks Other Products
- H3C Other Products
- NVIDIA Mellanox Cables
- Juniper Power Supply
- HPE Aruba Power Supplies
- HPE Aruba Accessories
- NVIDIA Mellanox Accessories
- Broadcom Accessories
- Ruijie Others
- Ruijie Power Supplies
- H3C Power Supplies, Cables and Other
- Power Supplies
- Huawei Licenses
- Modules & Cards
- Servers
- Rack Servers
- HPE ProLiant Gen9 Rack Servers
- HPE ProLiant Gen10 Rack Servers
- HPE ProLiant DL580 Gen10 Servers
- HPE ProLiant DL560 Gen10 Servers
- HPE ProLiant DL388 Gen10 Servers
- HPE ProLiant DL385 Gen10 Servers
- HPE ProLiant DL380 Gen10 Servers
- HPE ProLiant DL360 Gen10 Servers
- HPE ProLiant DL325 Gen10 Servers
- HPE ProLiant DL160 Gen10 Servers
- HPE ProLiant DL20 Gen10 Servers
- HPE ProLiant DL325 Gen10 Plus Servers
- HPE ProLiant DL385 Gen10 Plus Servers
- Dell PowerEdge Rack Server
- Dell PowerEdge R740 Server
- Dell PowerEdge R740xd Server
- Dell PowerEdge R640 Server
- Dell PowerEdge R540 Server
- Dell PowerEdge R440 Server
- Dell PowerEdge R340 Server
- Dell PowerEdge R240 Server
- Dell PowerEdge R840 Server
- Dell PowerEdge R940 Server
- Dell PowerEdge R230 Server
- Dell PowerEdge R330 Server
- Dell PowerEdge R430 Server
- Dell PowerEdge R530 Server
- Dell PowerEdge R620 Server
- Dell PowerEdge R630 Server
- Dell PowerEdge R730 Server
- Dell PowerEdge R730xd Server
- Dell PowerEdge R830 Server
- Dell PowerEdge R920 Server
- Dell PowerEdge R930 Server
- Dell PowerEdge R760 Server
- Dell PowerEdge R660 Server
- Inspur Rack Servers
- Huawei RH Series Rack Servers
- Lenovo Rack Servers
- H3C Rack Servers
- Tower Servers
- HPE ProLiant Gen9 Tower Servers
- HPE ProLiant Gen10 Tower Servers
- Dell PowerEdge Tower Servers
- Dell PowerEdge T640 Servers
- Dell PowerEdge T440 Servers
- Dell PowerEdge T340 servers
- Dell PowerEdge T140 servers
- Dell PowerEdge T30 servers
- Dell PowerEdge T130 servers
- Dell PowerEdge T330 servers
- Dell PowerEdge T430 servers
- Dell PowerEdge T630 servers
- Dell PowerEdge T40 Servers
- Dell PowerEdge T150 Servers
- Dell PowerEdge T350 Servers
- Dell PowerEdge T550 Servers
- Inspur Tower Servers
- Lenovo Tower Servers
- Blade Servers
- Server Systems
- Servers Processors
- Servers Hard Drives
- Server Memories
- Server Accessories
- Sever Modules & Cards
- Dell Servers
- Dell Tower Server
- Dell Rack Server
- Dell PowerEdge R740 Server
- Dell PowerEdge R740xd Server
- Dell PowerEdge R640 Server
- Dell PowerEdge R750 Server
- Dell PowerEdge R750xs Server
- Dell PowerEdge R750xa Server
- Dell PowerEdge R650 Server
- Dell PowerEdge R550 Server
- Dell PowerEdge R450 Server
- Dell PowerEdge R350 Server
- Dell PowerEdge R250 Server
- Dell PowerEdge XR11 Server
- Dell PowerEdge XR12 Server
- Dell PowerEdge R540 Server
- Dell PowerEdge R440 Server
- Dell PowerEdge R340 Server
- Dell PowerEdge R240 Server
- Dell PowerEdge R840 Server
- Dell PowerEdge R940 Server
- Dell PowerEdge R940xa Server
- Dell PowerEdge R6515 Server
- Dell PowerEdge R6525 Server
- Dell PowerEdge R7515 Server
- Dell PowerEdge R7525 Server
- Dell PowerEdge R230 Server
- Dell PowerEdge R330 Server
- Dell PowerEdge R430 Server
- Dell PowerEdge R530 Server
- Dell PowerEdge R620 Server
- Dell PowerEdge R630 Server
- Dell PowerEdge R730 Server
- Dell PowerEdge R730xd Server
- Dell PowerEdge R830 Server
- Dell PowerEdge R920 Server
- Dell PowerEdge R930 Server
- Dell PowerEdge R760 Server
- Dell PowerEdge R660 Server
- Dell Server Modules & Cards
- Dell AI Servers
- Dell Rack Servers
- Huawei Servers
- Lenovo Servers
- Lenovo Rack Servers
- Lenovo ThinkSystem SR570 Rack Servers
- Lenovo ThinkSystem SR530 Rack Servers
- Lenovo ThinkSystem SR550 Rack Servers
- Lenovo ThinkSystem SR590 Rack Servers
- Lenovo ThinkSystem SR650 Rack Servers
- Lenovo ThinkSystem SR850 Rack Servers
- Lenovo ThinkSystem SR860 Rack Servers
- Lenovo ThinkSystem SR258 Rack Servers
- Lenovo ThinkSystem SR588 Rack Servers
- Lenovo Tower Servers
- Lenovo Server Hard Disks
- Lenovo Server Memories
- Lenovo Server Power Supplies
- Lenovo Server Array Cards
- Lenovo Server Network Cards
- Lenovo Server HBA Cards
- Lenovo Server Hybrid Flash Arrays
- Lenovo Server Storage Accessories
- Lenovo Rack Servers
- Lenovo AI Servers
- Lenovo Rack Servers
- H3C Servers
- Inspur Servers
- HPE Servers
- HPE Rack Servers
- HPE ProLiant DL580 Gen9/10 Servers
- HPE ProLiant DL560 Gen9/10 Servers
- HPE ProLiant DL388 Gen9/10 Servers
- HPE ProLiant DL385 Gen10 Servers
- HPE ProLiant DL380 Gen10 Servers
- HPE ProLiant DL385 Gen10 Plus Servers
- HPE ProLiant DL360 Gen9/10 Servers
- HPE ProLiant DL325 Gen10 Servers
- HPE ProLiant DL325 Gen10 Plus Servers
- HPE ProLiant DL180 Gen9 Servers
- HPE ProLiant DL160 Gen9/10 Servers
- HPE ProLiant DL120 Gen9 Servers
- HPE ProLiant DL20 Gen9/10 Servers
- HPE ProLiant DL360 Gen10 Plus Servers
- HPE ProLiant DL380 Gen10 Plus Servers
- HPE ProLiant DL20 Gen9
- HPE Tower Servers
- HPE Blade Servers
- HPE Synergy 480 Gen10 Compute Modules
- HPE Synergy 660 Gen10 Compute Modules
- HPE Synergy 12000 Frame
- HPE Synergy 12000 Frame Power Options
- HPE Blade Server I/O Network Modules
- HPE ProLiant BL660c Server Blade
- HPE ProLiant BL460c Server Blade
- HPE ProLiant BL920s Server Blade
- HPE BladeSystem c3000
- HPE BladeSystem c7000
- HPE ProLiant WS460c Graphics Server Blade
- HPE Blade Server Mezzanine card/Network
- HPE Apollo Servers
- HPE Apollo r2200 Servers
- HPE Apollo r2600 Servers
- HPE Apollo r2800 Servers
- HPE Apollo 4200 Servers
- HPE Apollo 4510 Servers
- HPE Apollo 4520 Servers
- HPE Apollo 4530 Servers
- HPE Apollo 6000 Servers
- HPE Apollo k6000 Servers
- HPE Apollo d6500 Servers
- HPE ProLiant XL170r Servers
- HPE ProLiant XL190r Servers
- HPE ProLiant XL230k Servers
- HPE ProLiant XL450 Servers
- HPE Server Processors
- HPE DL20 Server Processors
- HPE DL120 Server Processors
- HPE DL160 Server Processors
- HPE DL180 Server Processors
- HPE DL360 Server Processors
- HPE DL380 Server Processors
- HPE DL385 Server Processors
- HPE DL560 Server Processors
- HPE DL580 Server Processors
- HPE ML30 Server Processors
- HPE ML110 Server Processors
- HPE ML150 Server Processors
- HPE ML350 Server Processors
- HPE BL460c Blade Server Processors
- HPE BL660c Blade Server Processors
- HPE Apollo Servers Processors
- HPE DL380 Server Processors
- HPE Server Hard Drives
- HPE Server Memories
- HPE Server Network Controllers
- HPE Server Storage Controllers
- HPE Server Licenses
- HPE Server Network Cards
- HPE Server Power Supplies
- HPE Server Accessories
- HPE AI Servers
- HPE Rack Servers
- Juniper Servers
- F5 Load Balancers
- xFusion Servers
- FusionServer 1288H V5 Rack Server
- FusionServer 1288H V6 Rack Server
- FusionServer 2288H V5 Rack Server
- FusionServer 2288H V6 Rack Server
- FusionServer 2488H V5 Rack Server
- FusionServer 2488H V6 Rack Server
- FusionServer 5288H V5 Rack Server
- FusionServer 5288H V6 Rack Server
- FusionServer 5885H V5 Rack Server
- FusionServer CX5200 V5 Server
- Rack Server
- Supermicro Servers
- Cisco Servers
- Kits
- ASUS Servers
- AI Server
- Rack Servers
- Storages
- Direct-Attached Storages DAS
- Network Attached Storages NAS
- Storage Area Network SAN Storages
- Hybrid Flash Storages
- SAN/DAS/NAS Storages
- Other Storages
- Storage Switches/Controllers
- Storage Transceivers/Modules/Cards
- Storage Licenses
- HPE Storages
- Inspur Storages
- Dell Storages
- Huawei Storages
- Synology Storages
- QNAP Storages
- Hitachi Storages
- Lenovo Storages
- NetApp Storages
- Video Surveillance
- IP Cameras
- Digital Video Recorders
- Network Video Recorders
- PTZ Cameras
- Dahua Video Surveillance
- Hikvision Video Surveillance
- Hikvision Network Cameras
- Hikvision IP Series Network Cameras
- Hikvision PanoVu Series Network Cameras
- Hikvision DeepinView Series Network Cameras
- Hikvision Explosion-Proof Series Network Cameras
- Hikvision Anti-Corrosion Series Network Cameras
- Hikvision AcuSense Series Network Cameras
- Hikvision Special Series Network Cameras
- Hikvision Pro (EasyIP) Series Network Cameras
- Hikvision ColorVu Series Network Cameras
- Hikvision Panoramic Series Network Cameras
- Hikvision Ultra (SmartIP) Series Network Cameras
- Hikvision Wi-Fi Series Network Cameras
- Hikvision Turbo HD Cameras
- Hikvision Analog Cameras
- Hikvision Digital Video Recorders
- Hikvision Network Video Recorders
- Hikvision PTZ
- Hikvision Thermal Cameras
- Hikvision Video Intercom
- Hikvision Access Control
- Hikvision HiLook Products
- Hikvision Mobile Products
- Hikvision Intelligent Traffic Products
- Hikvision Transmission and Display Products
- Hikvision Alarm Products
- Hikvision Other Products
- Hikvision Network Cameras
- Huawei Video Surveillance
- Video Surveillance Accessories
- Optical Access Network
- Huawei OLT
- Huawei ONT
- Huawei MDU
- ZTE PON OLT
- ZTE PON MDU
- ZTE PON ONT
- FiberHome OLT
- FiberHome MDU
- FiberHome GPON ONT
- Cisco Catalyst PON OLT
- Cisco Catalyst PON ONT
- Huawei Access Network
- Huawei OLT
- Huawei ONT
- Huawei MDU
- Huawei SmartAX EA5821 Series
- Huawei SmartAX MA561x Series
- Huawei SmartAX MA562x Series
- Huawei SmartAX MA5633 Series
- Huawei SmartAX MA567x Series
- Huawei SmartAX MA569x Series
- Huawei SmartAX MA58xx Series
- Huawei SmartAX MA5612 Series Boards
- Huawei SmartAX MA5616 Series Boards
- Huawei SmartAX MA5818 Series Boards
- Huawei Access Network Accessories
- Huawei Access Network Softwares
- Huawei OLT
- ZTE Optical Access Network
- FiberHome Optical Access Network
- Cisco Optical Access Network
- Optical Transmission Network
- Consumer
- Mikrotik
- Tenda
- Sonicwall
- Kingston
- Arista
- Palo Alto
- Ubiquiti
- NVIDIA Mellanox
- Ruckus
- Aruba
- Network Management
- Swtiches
- Cyber Security
- Security
- Ruijie
- Power supply
- Other
- controller
- H3C Wireless
- Power Supplies
- H3C
- Hillstone
- xFusion
- A10
- F5
- Palo Alto
- Check Point
- Supermicro
- Data Protection
- ASUS
- AI Workstation
Search